CNVD-2020-10487-Tomcat-Ajp-lfi.py#!/usr/bin/env python#CNVD-2020-10487 Tomcat-Ajp lfi#by ydhcuiimport struct# Some references:# https://tomcat.apache.org/connectors-doc/ajp/ajpv13a.htmldef pack_string(s): if s is Non...
2020-08-03 /
763 次浏览 /
核心成员
邪恶土豆MS16075 EXPhttps://pan.baidu.com/s/1O2tQg9AO0aWmWeIPvXv9oQ 提取码: 8v9aNC MS16032 MS13046 LCX 下载https://pan.baidu.com/s/1xEnJbrpmEsXIe0iwPjyDDA 提取码: 6ev2...
2020-08-03 /
849 次浏览 /
核心成员
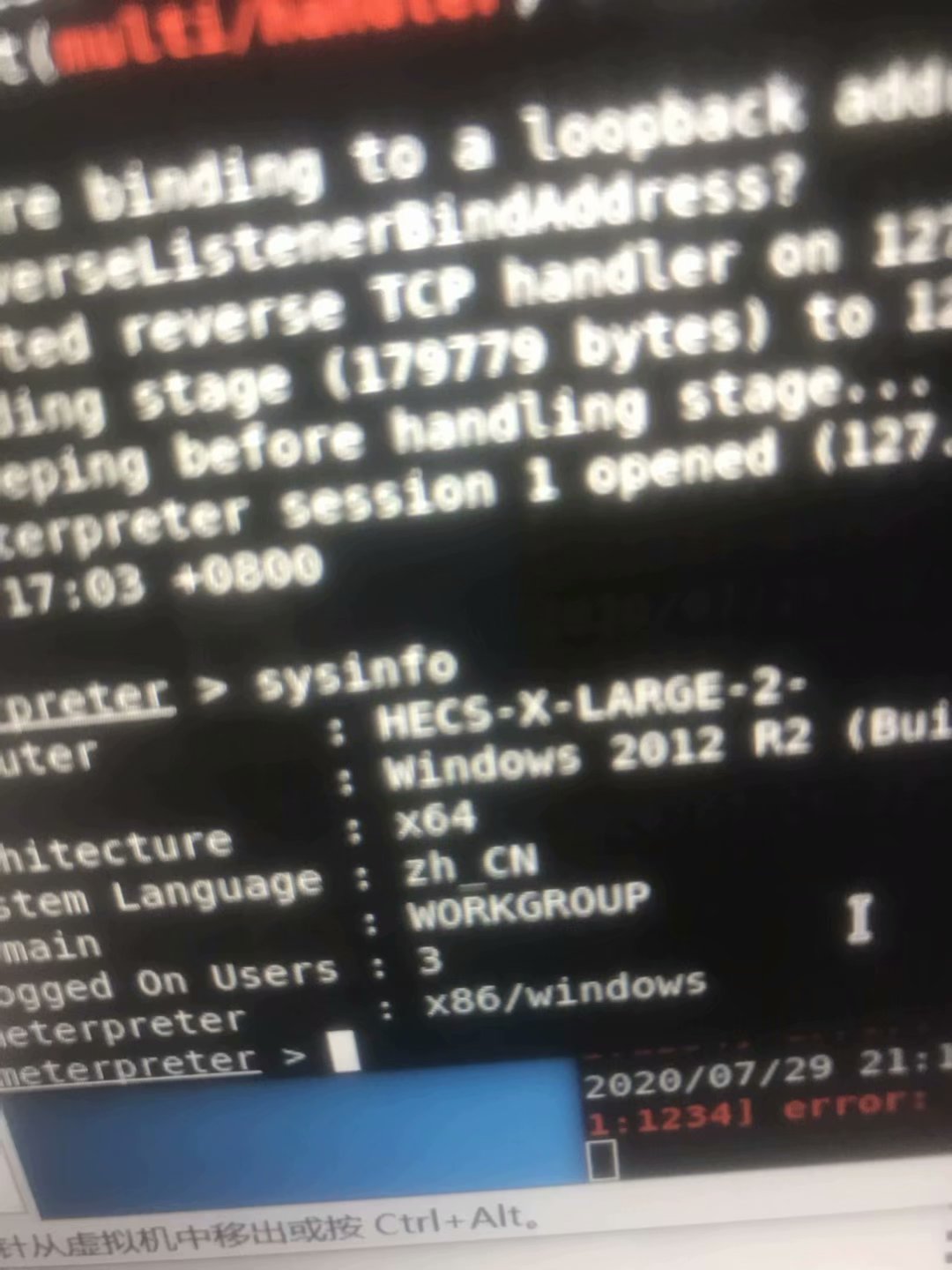
frp配合msf木马反弹,利用ms16075拿下windows2012服务器...
2020-08-03 /
983 次浏览 /
核心成员
针对从业安全行业的人员职业规划发展未来走向的建议目前国内几家大型IT安全公司,无外乎阿里巴巴,腾讯,360,中国网安,绿盟,启明星辰,天融信,安恒等当然也有一些大量的小型IT公司对于职业规划,方向,和发展,需要进行分析如果你只有25岁,那么可以考虑在大公司深造几年,转型管理如果你超过了30岁,那么可以积累管理经验,找一个相对好点的“甲方”单位进行铺垫根据收入,技术能力,以及发展方向的分析阿里巴巴:作为马云创办的阿里巴巴集团,在安全技术方面,在国内处于领先地位,主要工作地点:杭...
2020-06-30 /
902 次浏览 /
核心成员
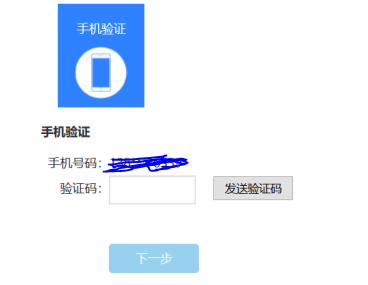
安恒玄武盾也有拦截不了的漏洞--逻辑漏洞因为大部分的扫描器是无法直接扫描出逻辑漏洞,所以玄武盾自然也就无法拦截逻辑漏洞逻辑漏洞通常需要对JS框架进行分析,最终分析出逻辑的走向,才能判断如何发掘逻辑漏洞上图为一个短信发送接口这时候可以利用的逻辑可以分为很多种一种是直接正常请求去获取用户参数一种是输入错误的验证码,进行逻辑绕过一种是通过逻辑触发XSS还有一种是非正常的请求获取用户参数思路可以是很多种,前提是利用的危害是什么这时候利用response修改的包,玄武盾是根本无法拦截的...
2020-06-14 /
1909 次浏览 /
核心成员
execCommand 处理Html数据js:<script>var ue = UE.getEditor('w0'); //编辑器 function insertHtml(val) { UE.getEditor('w0').execCommand('insertHtml', val); }...
2020-06-14 /
776 次浏览 /
业界新闻
揭开区块链渗透测试的神秘面纱区块链技术正在改变人们的工作和生活方式。凭借无与伦比的潜力,区块链使人们能够更好地控制和管理金融交易、医疗保健和许多其他活动,这些活动需要更多的隐私和透明度。以下帮助人们了解什么是区块链渗透测试。 2014年,全球规模最大的比特币交易所价值5亿美元的比特币被盗,此外大约有6,000万美元的以太币通过基于以太坊的分散式自治组织(DAO)重定向至匿名帐户。2017年,全球第二大比特币攻击事件发生在比特币在线交易平台Bitfinex,造成将近7200万...
2020-06-14 /
1015 次浏览 /
业界新闻
蚂蚁金服招聘应用和区块链等安全人才有意者请投递简历至:lizhong.blz@antfin.com蚂蚁金服期待你的加入。招聘岗位:应用安全专家岗位职责:1. 负责蚂蚁金服产品的安全需求评审,代码审计,安全测试,漏洞应急响应等工作;2. 负责蚂蚁相关应用框架、组件的漏洞挖掘、分析及漏洞应急响应;3. 负责蚂蚁应用安全能力建设(白盒代码扫描,交互式扫描,IDE安全插件等)4. 负责蚂蚁安全解决方案组件建设岗位要求:1. 成熟的SDL工作经验和落地经历2. 熟练...
2020-06-14 /
867 次浏览 /
业界新闻
玄猫安全实验室招聘渗透测试人才投递邮箱:lyon.chen@xuanmao.org(投递时邮件主题请包含投递的岗位名称,并注明来自安全客 ) 平台简介玄猫安全实验室专注于WEB安全、红蓝军攻防演练、漏洞挖掘、高级渗透测试、区块链安全等领域,团队成员来自于腾讯、阿里、360等国际顶尖安全团队,在国内网络安全领域拥有十年以上的从业经验团队。凭借卓越的技术实力和丰富的实战经验,已为数十家银行、保险、交易所、执法机关等提供基础安全建设、渗透测试、漏洞挖掘、应急响应等安全服务...
2020-06-14 /
929 次浏览 /
网络安全
注册信息安全专业人员CISP-PTE渗透测试工程师认证培训班组织形式指导单位:中国信息安全测评中心主办单位:北京中培伟业管理咨询有限公司 课程背景为提高各单位信息安全整体水平,加强信息安全人员专业技能,促进信息安全人员持证上岗,现组织开展注册信息安全专业人员攻防领域(CISP-PTE)培训及认证工作,此认证是信息安全从业人员的水平证书,证明证书持有者具备从事信息安全技术领域网站渗透测试工作,具有规划测试方案、 编写项目测试计划、编写测试用例、测试报告的基本知识和能力...
2020-06-14 /
798 次浏览 /
网络安全